Enterprise I.T. Infrastructure
Creating an agile platform for you to build your business on


Continuous innovation from Microsoft-supports your development today, and your product visions for tomorrow.

Continuous innovation from Microsoft-supports your development today, and your product visions for tomorrow.
Continuous innovation from Microsoft-supports your development today, and your product visions for tomorrow.
Continuous innovation from Microsoft-supports your development today, and your product visions for tomorrow.

Firewalls put up a barrier between your trusted internal network and untrusted outside networks, such as the Internet. You can implement a firewall in either hardware or software form, or a combination of both.
Email gateways are the number one threat vector for a security breach. A email security application blocks incoming attacks and controls outbound messages to prevent the loss of sensitive data.

Wireless security is the prevention of unauthorised access or damage to computers or data using wireless networks, including Wi-Fi networks.
BYOD can complicate your cybersecurity needs, but that doesn’t mean it is a bad idea. To help ensure your network stays secure there are some steps you should take and some policies you should consider implementing.

Network Access Control (NAC) is an approach to computer security that attempts to unify endpoint security technology (such as antivirus, host intrusion prevention, and vulnerability assessment), user or system authentication and network security enforcement.

Unsure where to start? Our expert team will help you plan the perfect technology foundations to build your business on, taking you through the myriad of options available.
Putting the plan into action we can refresh your existing infrastructure or start from scratch. This can be done to suit business requirements out of hours & in phases.

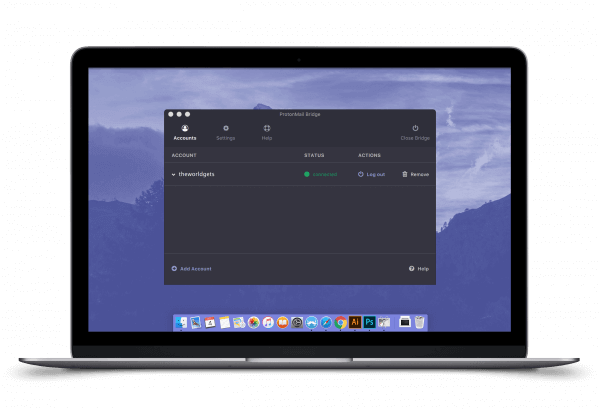
Once deployed, our Service Desk and team of Network Engineers will take over to ensure that everything is kept ticking along, enabling your business to succeed.
Get in touch with us at United Business Group today to see how we can help you create a seamless I.T. infrastructure for your employees, anywhere in the world.
Let Us Help